Staying compliant with the HIPAA Security Rule can be a daunting task. With ever-changing regulations and a complex set of requirements, it can be difficult to know where to begin. This article will provide an overview of the HIPAA Security Rule and explain how to ensure compliance with the law. We'll discuss topics such as the requirements of the rule, the steps you should take to comply, and the penalties for non-compliance.
By understanding the HIPAA Security Rule, you can make sure that your organization is doing its best to protect the privacy and security of its customers' information. The Health Insurance Portability and Accountability Act (HIPAA) Security Rule defines the standards for protecting PHI. It requires organizations to maintain administrative, physical, and technical safeguards to ensure that PHI is secure at all times. Administrative safeguards involve developing policies and procedures to ensure that PHI is properly managed. Organizations must also have a designated security official who is responsible for overseeing all security-related activities.
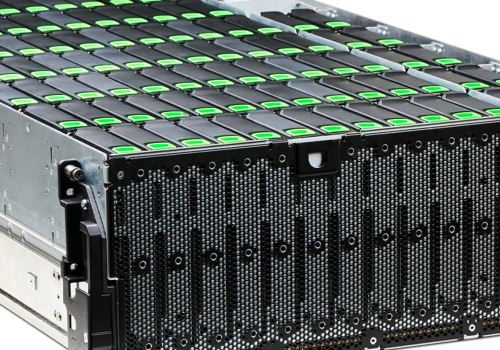
Physical safeguards are measures taken to protect PHI from unauthorized access and damage. These include securely storing hard copies of PHI and using access control measures such as locks, surveillance systems, and visitor logs.
Technical safeguards
involve using technologies such as encryption, firewalls, and passwords to protect PHI from unauthorized access. Organizations must also have policies in place to protect against malware, viruses, and other malicious software.Organizations must also have a process for responding to security incidents. This includes having a plan for reporting any potential security breaches, as well as having procedures in place to respond quickly and effectively.
Organizations must also provide training
to employees on the HIPAA Security Rule and other relevant privacy regulations. Additionally, they must ensure that all vendors who have access to PHI are compliant with the HIPAA Security Rule.Finally, organizations must regularly review their security measures to ensure they are up-to-date with the latest security standards. They must also monitor their systems for any potential security breaches or vulnerabilities.
Ensuring Compliance with the HIPAA Security Rule
In order to protect the privacy of their patients' health information, organizations must comply with the HIPAA Security Rule. Here are some steps organizations can take to ensure they are in compliance:Develop Policies and Procedures for Managing PHI - Organizations should develop policies and procedures for managing protected health information (PHI). These policies and procedures should include guidelines for storing, accessing, and sharing PHI.Designate a Security Official
- Organizations should designate a security official responsible for ensuring compliance with the HIPAA Security Rule.This individual should have a clear understanding of the organization's policies and procedures regarding PHI.
Use Physical Safeguards to Protect PHI
- Organizations should use physical safeguards to protect PHI, such as locked filing cabinets and restricted access to computer systems.Implement Technical Safeguards
- Organizations should implement technical safeguards such as data encryption, firewalls, and virus protection software.Have a Process for Responding to Security Incidents
- Organizations should have a process in place to respond to any security incidents. This process should include steps for investigating and reporting any incidents.Train Employees on Privacy Regulations
- Organizations should provide training to their employees on privacy regulations. This training should include information on how to handle PHI responsibly.Ensure Vendors Are Compliant with the HIPAA Security Rule
- Organizations should ensure that any third-party vendors they work with are compliant with the HIPAA Security Rule. This includes conducting due diligence when selecting vendors.Regularly Review Security Measures
- Organizations should regularly review their security measures to ensure they are adequate.This includes testing for vulnerabilities and patching any identified weaknesses.
Monitor Systems for Potential Vulnerabilities
- Organizations should monitor their systems for potential vulnerabilities. This may include using automated tools to detect suspicious activity. Ultimately, compliance with the HIPAA Security Rule is essential for any organization that handles protected health information. Organizations must have adequate administrative, physical, and technical safeguards in place, as well as a process for responding to security incidents and regular reviews of their security measures. Additionally, employees must be trained on privacy regulations.By following these guidelines, organizations can ensure that they remain compliant with the HIPAA Security Rule.







Leave Message